In a time when Internet connectivity is so important, manufacturers have met this demand by creating products that feature the ability to connect to apps or other Internet-based dashboards. Unfortunately for users, there is a lot that can go wrong when organizational practices don’t do enough to protect their customer’s privacy; or, simply look to exploit it. Let’s take a look at how the smart devices you depend on can be undermining your family’s privacy.
Argentum IT LLC Blog
When it comes to cybersecurity, businesses have a lot to keep tabs on—even a small business like yours. In fact, you wouldn’t believe just how much goes into cybersecurity and why your organization needs to make it a priority. Today, we want to convince you that cybersecurity is more than just a buzzword on the Internet; it’s a lifeline that will keep your company secure.
There are a few occasions that we get a very apparent example of how important basic cybersecurity is, regardless of where you are, and this year’s National Football League draft is one such example.
For those who don’t follow the NFL or the draft proceedings, multiple draftees received prank calls during the process, although one in particular is applicable to businesses of all kinds. Let’s examine this situation to reinforce a few critical cybersecurity best practices.
We’ve all had to confirm we’re not a computer when attempting to log into an account. This is the core purpose of what once was called CAPTCHA… the Completely Automated Public Turing test to tell Computers and Humans Apart. However, it seems surprising that computers don’t easily overcome these simple-seeming tests.
Let’s dig into why these simple tests actually are effective at differentiating between human users and automated bots.
Your Android device offers a lot of capabilities in its little frame, with many people relying on theirs to keep their lives organized and generally handled. Many businesses even rely on Android mobile devices. This should only reinforce how critical privacy and security are.
In light of this, we’ve shared a few simple tips anyone can do to help make a smartphone that much more secure.
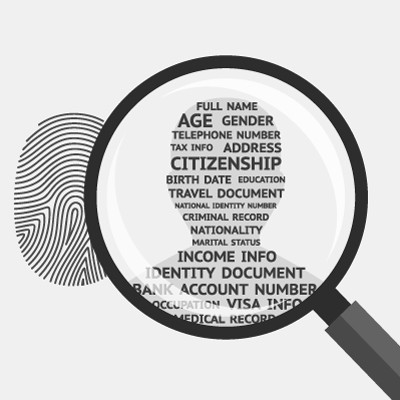
Since so much of the world is now online, businesses and organizations interact with people online now more than ever. This means they also collect people’s information, a practice they do for various reasons. Individuals need to consider their own data privacy and how it might be affected by business practices.
X The Everything App®, formerly Twitter, has been experiencing a massive user loss for the past few weeks, with everyone from celebrities to average people evacuating from the platform. If you wish to join them for any reason, we’re sharing the process for fully extricating yourself and your data from this specific social media network.
In recent years, there has been much debate about how companies collect, sell, and use personal data. Many businesses make extra money by selling data they collect about people. This might seem like a side effect of all the data we create online, but it can lead to some tricky problems. Today, we'll look at something called the "data-broker loophole," how it works, and what we can do about it.
Modern wisdom states that if you’re not paying for a product, you’re the product.
For all the good the Internet is capable of doing, it is equally capable of being extremely harmful… especially when data is involved. Websites and social media platforms collect data from their users and track their movements across the Internet, sell it to advertisers, and more recently, use it to train AI.
Let’s go over what you can—and arguably should—do to limit these platforms' ability to do so.
These days, data privacy is absolutely critical in both a business and individual context. In some locations, governments have introduced legislation to protect consumers, and in others, there is significant pushback in favor of fewer regulations on business. How does data privacy factor into your business’ operations?
In 2004, a service called VirusTotal was launched and swiftly became a popular antivirus and malware scanner to help detect threats in various files and URLs. It became popular enough that it was officially acquired by Google in 2012 and ultimately assimilated into Chronicle, a cloud-based security operations suite for enterprise businesses. Despite this impressive pedigree, however, we find ourselves able to look to VirusTotal as a sobering reminder of how fickle cybersecurity can be, with the service being the source of some limited data exposure.
Compliance is a critical element of many businesses’ requirements, with pretty severe penalties as a consequence if the prescribed standards are not met. Even more importantly, most compliance requirements and regulations are put in place for the welfare of not only the business, but its clientele as well. This makes it critical to know which apply to your business, and how to meet them fully.
When it comes to security, one often overlooked tool is the virtual private network, or VPN. We recommend that all businesses use a VPN to keep remote and hybrid workers from inadvertently putting your business’ data at risk while out of the office. Let’s go over why a VPN is so effective, as well as what you should look for in a business-grade VPN tool.
Who are you? While it’s a question that’s been asked in all contexts with all levels of metaphysicality attached—from asking someone their name to prompting someone to follow a path of spiritual self-discovery—the growth of the metaverse once again urges us to ask it in a more literal way. When accessing a conglomeration of various services and platforms, how many identities will each user need to juggle?
We aren’t going to try and pretend that the investments necessary to preserve your business’ data security are small ones. Especially at first glance, you may very well start to question if such an investment is truly necessary.
The simple fact of the matter is that, compared to the costs that a breach of privacy will incur, the investment you put into your security measures will suddenly seem like a real bargain.
Chances are, you’ve gone through some old files and weeded through them, deleting what is no longer needed. This is especially important when you are upgrading your storage and getting rid of your existing storage media or an old computer. Let’s talk about what really happens when you’re doing so—chances are, you may be overlooking a serious security issue.
Have you ever wondered how some platforms will only have you log in once for all of your various needs, even though they might be different applications, websites, or services? This is essentially what single sign-on is, and it’s quite common in the technology world today. What is single sign-on exactly, and what kind of security does it actually provide for organizations that use it?
When we talk about data privacy in a business, the default is to generally think about the data the business has collected and compiled from its clientele. However, that’s just one type of data a business has. There’s also a lot of data that is collected by the business about that business’ employees. So, how well protected is this data?
With so many employees still working remotely, organizations have turned to technology to ensure that their workers are actually… you know, working. While the need to know what your employees are up to throughout the workday is important, there is now a discussion happening on whether or not this violates employees’ privacy.